Configure IPSec VPN Between PFSense and vCloud 10.2.2
Configuring an IPSec VPN on vCloud Director is easier than ever. Here’s a quick run through of how to do it with a PFSense firewall.
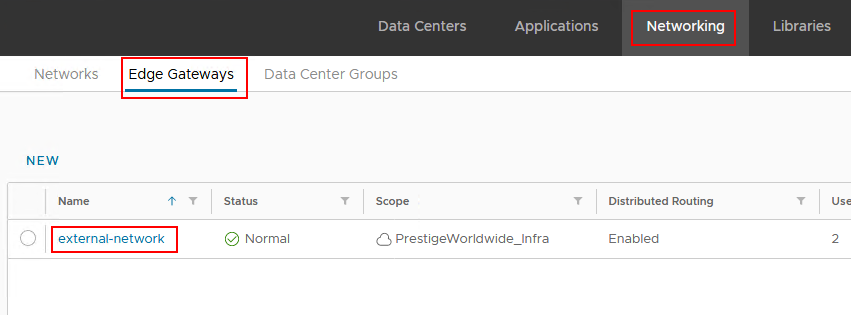
In vCloud, navigate to Networking > Edge Gateways and select your edge gateway.
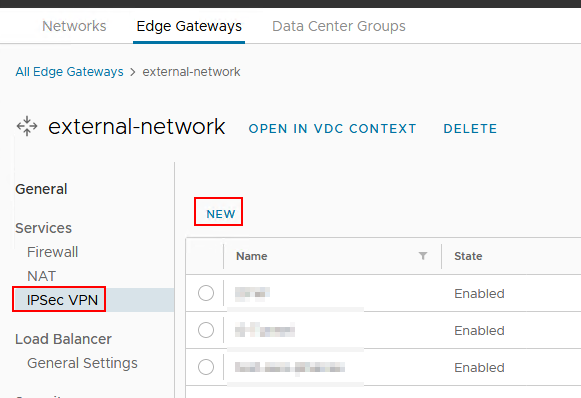
Then, go to IPSec VPN and click New
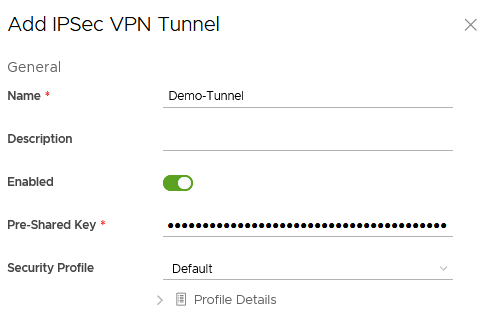
Fill out the form with Name, Description, and create your own pre-shared key (simply make something up, or use https://www.pskgen.com/).
The Local Endpoint IP Address is the IP address of your edge gateway. You can view available IPs by clicking the little (i) icon if you forget what that IP is. In my environment, this is a NAT IP, not the actual external IP.
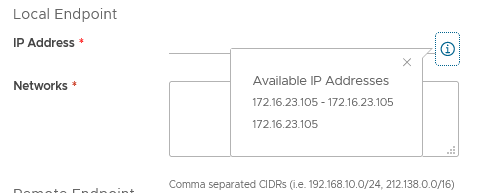
Enter the Local IP and local subnet that you want the VPN to connect to.
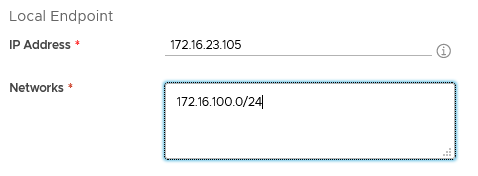
Under Remote Endpoint, enter the IP of your PFSense firewall and the networks on the PFSense side of the VPN.
Click Save and that’s really all there is to the vCloud configuration.
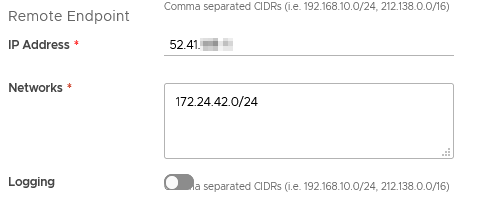
Now, in PF Sense, go to VPN > IPSec
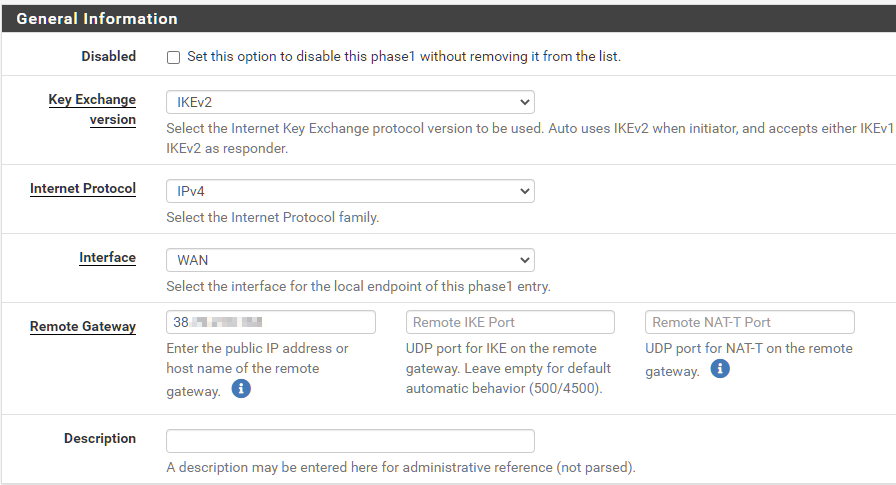
Click Add P1. In general, we will use the default settings for everything.
Under General Information > Remote Gateway, enter the public IP of your vCloud Edge Gateway (not the NAT IP, if your edge gateway is using a NAT.)
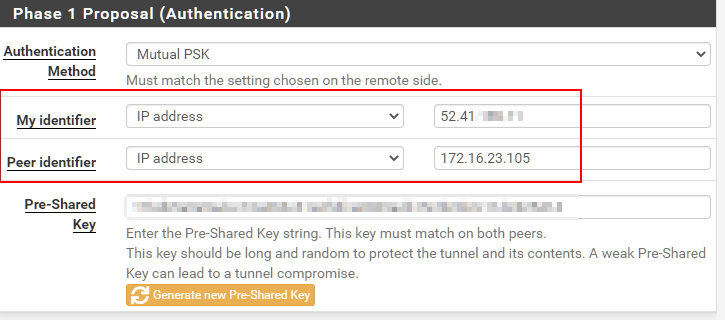
This is the trickiest part of the whole setup. Under Phase 1 Proposal (Authentication), you will need to set “My Identifier” to the PF Sense Public IP and the “Peer Identifier” to the Edge Gateway IP as defined as the Local Endpoint in vCloud Director. So if the Edge Gateway is using a NAT, put the NAT address here. In both settings, choose “IP address” from the dropdown. Enter the Pre-Shared Key in the appropriate box.
Leave the remaining settings as default, scroll to the bottom and click Save.
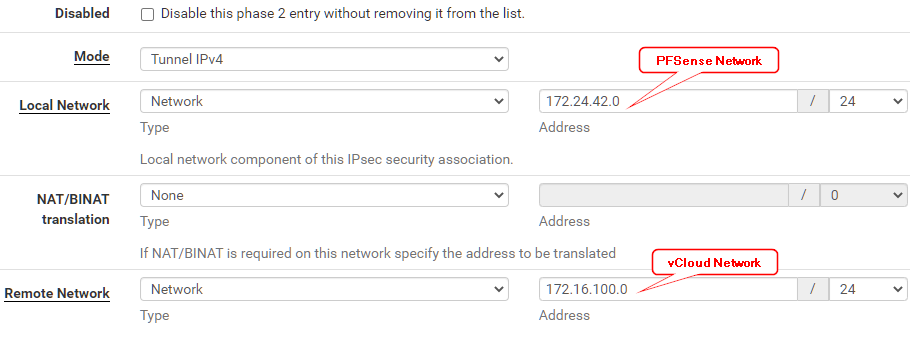
Under your new Tunnel, click Show Phase 2 Entries, then Add P2. This is where we define the local and remote subnets for the tunnel, and should match what we put in vCloud Director.
Under Local Network, choose Network from the drop down, then enter the PFSense network. Under Remote Network, enter the vCloud network.
Leave the rest default, scroll down and click Save.
Click “Enable” on your new Tunnel. Then click Apply Changes.
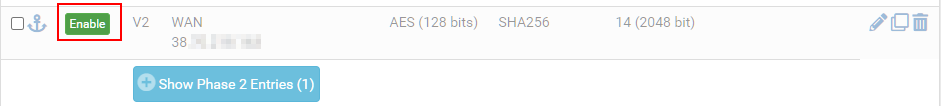
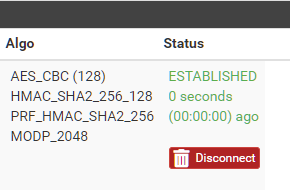
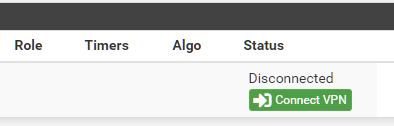
Then go to Status > IPSec and click Connect VPN.
And you should be good to go!